Minting as the New Web3 Currency: A Quick List of Popular Use Cases
The history of minting has traditionally been associated with governments creating and stamping official currency.
Enter the blockchain, and the essence of minting has found a new life, helping create and permanently record the genesis of “something new” (not money) on a given distributed ledger. Initially, we minted fungible cryptocurrency tokens, the first of which was Bitcoin. Later, around 2018, artists and producers began minting millions of Non-Fungible Tokens (NFTs), which they then sold to enthusiastic users.
With Web3 adoption now accelerating, minting is solidifying its place as a native action with an amazing array of versatile uses that will gradually challenge the widely used social media actions "Like," "Share," and "Subscribe."
While early Web3 adopters are taking minting like a duck to water, this concept has barely made a dent in the minds of Web2 users who represent a large target market.
The following table aims to demystify what minting is about, hopefully making the concept more comprehensible to a larger audience.
Intent | Benefit / Outcome | Examples |
Full Ownership | Full ownership of an NFT | That’s the most straightforward outcome of a mint action, and we got started. A given artist collection becomes available with a limited minting inventory, and they |
Partial Ownership | Supporting action | Supporting artists or creators by minting fractional ownership or right to their work either before the work is completed or after it is delivered. If done before availability, it’s like an advance, a micro-funding, or a Kickstarter-like support of sorts. |
Benevolent Donation | Patronage action | Users receive a certificate of support or a symbolic NFT as a proxy for having supported some work. You don’t receive anything of value in return, and there are no expectation of benefits, but you are supporting the creator by sending them some amount to support their work. |
Reward | Earn-to-receive | You’ve contributed toward something and therefore earned the right to mint (own) a given NFT, and sometimes you may receive a non-transferable token depicting that reward. |
Access Right | Token-gated content or services | If you own a given token or a certain quantity of it, you are granted automatic access to some gated content or work, after connecting your wallet to verify such credentials. It could be for a one-time access or ongoing membership access. |
Tipping | Good old tipping | Something impressed you, and you offered a tip in one click. There is no ownership of anything involved, but you are rewarding the creator with a symbolic token of your appreciation. |
Attestation | Permanent proof of something | Hey, I did this, and here’s proof of it that is permanently etched in the blockchain memory. For example, I’ve been using Receipts to track my fitness activity, and they let me mint (for free) the end-result of my running activity to-date (over a 6-week timeframe). Here’s an example of it below. |

The New Web3 Signal
Minting is destined to become a significant social signal in the emerging Web3 world. But it’s not just similar to a Like or a Share. Likes and Shares don’t cost you anything, and sometimes they are not even genuine. Minting signals have more “skin-in-the-game” or “sense of belonging”; and they will cost you something. Based on the above use case, one could argue they are more similar to a continuous Subscribe or “Support”.
We don’t stress over paying monthly fees for broadband Internet access, a premium ChatGPT service, or a given newspaper subscription. So why not acknowledge that being involved in blockchain will also entail a little monthly budget for minting this or that?
Eventually, the collection of our minting actions will form an interesting body of content, some of which will typify a permanent bookmark, a footprint, a journey, a memory, or a breadcrumb left behind.
It is now necessary for the rest of the world to comprehend minting.
As the cost of minting continues to drop to almost insignificant levels, the applications for minting are only beginning to be explored. The creativity of the avant-garde blockchain community—often referred to colloquially as the "Degens"—is boundless. As this community continues to experiment and innovate, we can expect to see minting applied in ever more creative and impactful ways, further cementing its role as a foundational action for Web3.
Without a doubt, minting will develop into a new social signal and an everyday pastime when browsing blockchain-oriented destinations. To see minting actions flow like a river, just visit Zora or Warpcast.
Soon enough, “what have you minted lately” will become a dinner table conversation.
The Rise of the Ridiculous? What Makes Memecoins Work: Community, Utility, and Mojo

The curious case of memecoins has re-emerged in full force. In the eyes of an outsider, memecoins thrive on virality, cultural statements, and sometimes a dose of absurdity. But beneath the veneer of internet jokes and dog-themed logos lies a surprisingly potent recipe for success.
Looking back at the past few years of memecoins, what lessons can we draw? Three interdependent qualities—Mojo, Community, and Utility—are central to their path.
Each element is not only fundamental on its own but also serves as a stepping stone to the next, creating a dynamic environment that fuels the rise and endurance of these digital currencies.
Mojo: The Spark of Virality
Mojo, in the context of memecoins, refers to the unique appeal or charisma that captures the imagination of the digital populace right from the get-go. It is the initial spark that sets the stage for virality. This characteristic is often rooted in humor, irony, or a direct challenge to conventional financial wisdom, which resonates with a broad audience looking for alternative investment opportunities or simply participating in a cultural movement. For example, Dogecoin, one of the most successful memecoins, started as a joke based on a popular internet meme. Its light-hearted origin story and the whimsical Shiba Inu mascot immediately caught the attention of internet users, granting it an instant 'mojo'. This appeal is critical for breaking through the noise of the cryptocurrency market and securing a spot in the collective digital consciousness.
Mojo is typically captured almost instantly. Either you have it or you don’t.
Community: The Growth Engine
While crucial for initial traction, a dedicated community must nurture and amplify a memecoin's mojo in order to maintain momentum. The community is not just a group of investors; it's a vibrant collective of believers, builders, creators, and promoters who embody the coin's ethos. They engage in discussions, develop capabilities, create content, and spread the word, thereby weaving the coin into the fabric of digital culture. The community's strength lies in its ability to mobilize quickly, influence market sentiment, and attract new members, thus propelling the memecoin to new heights. These early adopters become fervent evangelists, spreading the word on social media platforms like Reddit, X or Warpcast. The role of social media platforms cannot be overstated in this context, as they serve as the primary arenas for community interaction and growth. This online buzz creates a network effect, attracting new investors and driving up the price of the coin. The Dogecoin community, for example, has been known for its charitable initiatives and massive online campaigns, further solidifying its presence and attracting even more followers.
Utility: The Legitimization Factor
However, the meme coin magic doesn't need to stop at virality and community. As a memecoin matures, the need for utility—real-world applications and value—becomes increasingly apparent. This is where the transition from a purely speculative asset to a more stabilized cryptocurrency takes place. Utility can take various forms, such as integration into payment systems, partnerships with companies, or use in decentralized finance (DeFi) applications. This characteristic is crucial for long-term viability, as it provides a foundation beyond speculative trading, grounding the coin in tangible value. It also represents the final transformation of the memecoin from a cultural phenomenon to an established part of the cryptocurrency ecosystem.
Embracing Creativity as the Ultimate Objective?
It's important to note the sequential nature of the above three success factors.
Mojo attracts the initial buzz, piques everyone's interests, captures the imagination, and fosters a community that will amplify mindshare growth, and sustain the buzz. Eventually, the community will push for, and ultimately define, the coin's utility, cementing the coin's place in the digital economy. Although some coins survive on mojo, community support, and a smudgeon of silly utility, without a strong community, the initial spark of mojo can quickly fade, leaving the meme coin a relic of internet history.
“Utility” in the case of memecoins can be loosely defined. It is not as strict as commonly seen in the infrastructure layers of the blockchain where the token is responsible for the security of the network and finds itself as an essential element of transactional, mining, or staking activities. That said, some newer memecoins such as DEGEN, have gone a step further and launched their own sidechain which is a giant step in the world of utility.
The progression toward this trifecta, while not guaranteed for every memecoin, outlines a pathway to success that blends cultural resonance with economic value. As the digital cryptocurrency landscape continues to evolve, the role of these three characteristics in the success of memecoins will undoubtedly be a fascinating area for observation and study.
Whatever the case may be, creativity, originality, and self-expressiveness are common features of all these memecoins.
Let’s continue to hope that memecoin's creativity and innovative spirits get applied in the right direction.
Breaking from Silos: The Rise of Portable Messaging in Web3
For years, we've enjoyed the convenience of portable email. Thanks to the Simple Mail Transfer Protocol standard (SMTP), we can access our messages from any email client, anywhere in the world, because mail servers and message transfer services send and receive those messages in a standard way. This allows us to read emails on a phone, continue on a desktop or tablet, or sign in from anywhere with our credentials. This sounds boring because we have become used to it and take it for granted.
Let’s explore how this translates into the burgeoning world of Web3, where interactions take place between blockchain accounts and not email addresses.
Enter XMTP (Extensible Message Transport Protocol), a new messaging protocol designed specifically for Web3 applications, wallets, or anyone requiring streamlined communications between blockchain accounts.
As Web3 gains traction, blockchain clients—often mobile wallets or apps—are increasingly adding messaging features similar to what we see today in popular platforms like WhatsApp, Signal, Telegram, or Messenger. This has fostered a new wave of applications seamlessly combining wallet and messaging functionality, such as Converse or Family. Existing wallets like Coinbase’s have also jumped on the bandwagon by integrating messaging into their products.
The real game-changer with XMTP lies in its ability to facilitate the flow of messages across different Web3 platforms. Imagine you are a user on the Coinbase wallet interacting with its messaging feature, and you are also on Converse, a more focused messaging app. XMTP is that magic sauce behind the scenes, enabling seamless, real-time message synchronicity between those two apps. That sounds boring again, because you might think, Why not?
Not so fast, because this is not possible today in the current realm of messaging apps that dominate the market. You can’t send a message to a contact from WhatsApp and then reply to it from Signal or ping a friend on Messenger, and then continue the conversation on Telegram. Our friends don't always use the same messaging platforms as we do, so we end up following them wherever they are. In the Web3 world, XMTP lets users choose whatever messaging platform they prefer without compromising on the seamless aspect of communication.
Unlike their SMTP-based email client counterparts, the new Web3 XMTP-based messaging clients are lightweight, and some cater to specific use cases or application segments. As users, we will likely end up using a variety of Web3 clients or applications, depending on the situation. For those supporting XMTP, their users won’t have to worry about losing the aggregated synchronicity they were used to in regular email. This approach aligns perfectly with Web3's core principle of composability, which is another fancy word for interoperability and compatibility across platforms.
This is only one chapter in the story of Web3 messaging. We can expect that increased XMTP adoption will give birth to powerful new capabilities and functionalities, beyond what today's messaging platforms offer us. Currently, XMTP boasts almost 2 million reachable identities across a variety of client apps, which isn’t a big number when compared to the 3 billion+ global users on messaging platforms. But in the realm of Web3, that is a very respectable size to grow from.
One artifact of this evolution is the exploding popularity of Frames, a Warpcast innovation that is bringing onchain applications into social media and is poised to usher in a new level of “interactivity inside messaging” not seen before. Frames readily integrates with Web3 messaging platforms because XMTP supports it. Frames is taking user interactions to a new level, paving the way toward unforeseen possibilities.
But we are still at Ground Zero. The inception of Web3 messaging marks a significant milestone in the evolution of digital communication, and it is the dawn of a new era. This era is going to be characterized by enhanced interoperability, user autonomy, and innovation in interaction modalities, signifying a shift in how we initiate and participate in digital communications.
So buckle up and welcome to Web3 messaging. The current Web messaging is going to look so stale and old school very soon. Get ready to witness a revolution in communication that prioritizes user choice and independence from big Web2 brands, and fosters an interconnected and seamless Web3 user experience that is destined to rival its Web2 counterpart.
Ending footnote: XMTP is as secure as what we are currently used to. XMTP uses Messaging Layer Security (MLS), another new standard for end-to-end encryption (E2EE), allowing for secure messaging between different platforms. Google recently announced their MLS support.
Moving My Blog to Paragraph While Backing Into Web3
For most of us, Web3 is still a nebulous thing that we can't define or point to, despite its arrival being promised more than a few years ago.
In November 2020, I published a blog post titled There is no Web3...Until There is One. In it, I wrote, "...until the patchwork of Web 3.0 technologies finds itself inside mainstream applications that have a broad and large market reach potential, we will not have a Web 3.0 yet."
One of the problems with Web3 was that it remained in the technical realm of usage by early adopters. There were lots of friction and self-assembly requirements to knit the various pieces together to get a sense of "aha."
There has been progress since then.
On the surface, Paragraph looks like a Substack of sorts. Underneath it lie several Web3 features that reveal themselves, but only if you want them. There is no forcing anything on anyone. You can simply read this blog as you did when it was WordPress-published and Mailchimp or Feedblitz-delivered previously.
I am not going to get into all the Web3 features at once, but suffice to say that you first need to connect your Ethereum wallet to Paragraph, and the magic will unravel. I chose the Coinbase wallet because it lets me write on Paragraph from a desktop or my mobile phone (I finished editing this post on my phone, but started it on desktop). You can think of your wallet as the trigger to identify yourself to the App, a bit similar to when you go through a Google-powered authentication.
Some of these "Web3" features include:
Content Options. Each of these posts is part of a limited-edition collectible set of 10 that is available for $2.50 from any reader. Basically, you can own an NFT of this post, and only 10 will be minted. In the future, subscription memberships could be offered. I don't intend on doing that for now, but other authors might like that option. Going further, imagine that some specific content could be unlocked only if a certain NFT or token is present in your wallet. This feature is called "token-gated access," and I could invoke it in the future by issuing readers the $WAM token that was part of a Social Money Experiment I announced in June 2020, but I didn't have a lot of useful options for its usage then.
Distribution. Behind the scenes, Paragraph is integrated via the emerging messaging standard XMTP (an analog to the SMTP email standard), enabling you to receive this content straight into your Web3 wallet if it supports messaging, such as in the Converse App that I'm adopting now as my standard Web3 Messaging App. You can find me at wamougayar.eth, my ENS (Ethereum Name Service) profile. In addition, Paragraph is integrated with Farcaster, the decentralized social network beloved by early Web3 adopters. So, when I share this post on Warpcast (the Farcaster client anyone can use), you can subscribe via one-click or read it without leaving that app. And from the Web2 side, Paragraph is also integrated with SendGrid for email distribution, so I don't need to worry about using Feedblitz anymore. It took me 3 minutes to export my subscriber emails to Paragraph.

There is more to Web3 than what I've described above, but using these 5 things together gives you a glimpse at a future where the whole is going to be bigger than the sum of those parts: Paragraph, Warpcast, XMTP, my ENS identity, and Converse.
It's not all perfect, but it's coming together perfectly well, because I didn't have to do one technical thing to connect these 5 services together, except for a few clicks, just as every Web2 user is accustomed to doing.
This makes one wonder if, after all, at least initially, Web3 could become a bunch of features for Web2 experiences, in essence backing its way into adoption. It wouldn't be a bad thing. There are 5.3 billion Web2 users, and Web3 will chip at them slowly and gradually.
Welcome to the (real) emerging world of Web3. It has finally arrived in such a way that I am going to continue writing more about it.
Is Web3's Culture and Technology Enough to Expand the Blockchain Market on Their Own?
The core blockchain sector should reevaluate whether they believe they can independently onboard the next millions or billions of consumers.
I relate to a section from Gavin Wood’s Polkadot 2023 Roundup.
“…the failings of certain individuals who seem to think the messaging and marketability of Web3 can be successfully divorced from its technology and culture,” was Gavin's explanation for the crypto winter.
Although I agree with the first paragraph about the "failings of certain individuals," I don't think the mismatch between Web3 culture and marketing messaging is to blame.
Rather, there's a mismatch between the go-to-market strategy of the Web3 culture and the realities of customer adoption.
Web3’s technology and culture have been challenged in their own ways pertaining to their messaging and marketability. More than ten years into the birth of this industry, we still can’t point to a mainstream-class application with millions of daily or even weekly active users (not counting exchanges or wallets).
Web3 is reaching a wall in terms of user expansion because of subpar user experiences, as I've previously written, We Need Web2 User Experience To Get Us to Web3, Not Blockchain Protocols.
There is too much attention on the infrastructure players, yet they aren’t the ones that will ultimately own the consumer experiences.
Most L1 blockchain infrastructure teams are relatively small businesses (at the most, less than 250 in headcount). It is very difficult for them to wage multiple battles at once. First, they are fighting each other for mindshare and marketing messages to get attention. Second, they are continuously focused on herding people to develop and evolve their technologies. Thirdly, they must work very hard to draw in developers and users to reach significant adoption.
It’s difficult to execute all three parts well unless the surrounding ecosystem has expanded significantly to the point that, in the event of the central entity’s disappearance, the ecosystem as a whole would continue to advance with little to no harm.
Few infrastructure protocols are as (organizationally) decentralized as the ethos they evangelize to be enabling. Except for Bitcoin, most Foundations (or Labs) organizations continue to act as the main locomotive that pulls the whole train forward. Perhaps Ethereum comes in a close second due to the ongoing self-effacing nature of the Ethereum Foundation, whose role has shrunk considerably in relative terms compared to what the ecosystem is delivering.
Since adoption is the one factor that matters in terms of success, let's return to it.
So, how will the remaining millions (and billions) of users be drawn to crypto and the blockchain?
Within the current landscape of Web3 apps, the mainstream user will be hard-pressed to get excited and take on current Web3 apps like duck to water because there is too much of a jump to get into crypto with both feet and expect to figure things out.
Consequently, we shouldn’t be disparaging app efforts posing as Web2-first. When paired with a Web3 aftertaste, Web2 apps make a delicious appetizer.
I’m excluding “users” that speculate on cryptocurrency prices because, for many of them, central exchanges will give them user-friendly capabilities.
Infrastructure developers currently dominate the blockchain industry, but to attract application-first developers, we need to increase the number of developer-friendly services available.
Web3 and Web2 need each other. Let’s admit it.
The Web3 culture and technology have given us an incredible vision. But they need help in realizing it.
We Need Web2 User Experience To Get Us to Web3, Not Blockchain Protocols
To unleash blockchain's creativity, awkwardness and quirks in the Web3 user experience must be fixed.
There is a joke in tech circles that "if the user experience is bad, it must be Web3."
While the focus on incorporating blockchain technology is a priority, there is a growing concern that, in the pursuit of this innovation, valuable lessons learned from Web2 in terms of user interface (UI) design are being overlooked. This oversight is hindering the broader adoption of this new technology.
Web3 should embrace proven user experience (UX) practices from Web2 rather than reinvent the wheel, ensuring a more familiar and user-friendly transition into the next phase of the internet. If they don’t, they risk alienating mainstream consumers and creating products accessible only to a small, tech-savvy niche of crypto natives.
Years have been spent painstakingly creating fluid and understandable user interfaces for Web2 and mobile applications. It has been demonstrated that clarity and simplicity deliver engaging and productive user experiences. These principles have resulted in billions of users flocking to social media platforms, content destinations, travel services, streaming venues, and e-commerce giants.
The allure of Web3 espouses a radical departure from the norms of established Web paradigms. However, the shift to blockchain technology, decentralization, and cryptographic ownership should not come at the expense of user experience.
Here are three reasons why Web3 needs more Web2:
The average user prioritizes usability over blockchain technology. Complex onboarding processes, jargon-filled interfaces, and lack of intuitive navigation hinder adoption and alienate them.
Familiarity with Web2 interfaces fosters trust and engagement, enhancing comfort and security for users entering the Web3 space, promoting further exploration and engagement.
Simplicity and clarity are key for promoting accessibility to a wider audience. Web3's decentralized nature is innovative, but its user interface doesn't have to reinvent the wheel.
Amidst the majority of Web3 apps that have no chance of gaining mainstream adoption, there is a new generation of apps that are not so smitten by Web3 geekiness and prioritize Web2 ease of use instead. Here is a sample.
In the dining category, Blackbird looks like a restaurant loyalty app to the user. Somewhere in its technology structure, blockchain magic enables unique, non-transferable badges (NFT-based) that users earn as a visit counter. There is also a private cryptocurrency akin to airline miles that can be exchanged for restaurant perks, all with very little transaction friction.
In decentralized finance (DeFi) where apps tilt on crypto nerdiness, Prime is a cross-chain prime brokerage service that lets users deposit, borrow, repay, and withdraw cryptocurrency across 8 different chains seamlessly. This sounds like a boring trait in traditional finance because currency fluidity is taken for granted (though at the cost of a lot of inner friction). In the blockchain world, Prime represents an advanced level of tucking-in interoperability across blockchains while hiding it from the user.
In social media, Warpcast looks almost exactly like Twitter (now known as X), but behind the scenes lies a social network protocol with a few web3 features such as blockchain-based identity, encrypted authentication, and decentralized data that the casual user need not worry about unless they want to. The initial experience is very mainstream Web2, while the platform gently surfaces Web3 snippets.
In the sports fantasy world, Silks lets you take ownership of a jockey, a horse, and land for your stables. The most interesting aspect is a synthetic 1:1 linkage from your fantasy (NFT) horse to a real one that could be racing at the Kentucky Derby, Belmont Stakes, or other known races. No one else owns that relationship. You can follow the real horse’s activity via a virtual stable dashboard on Equibase. When the horse wins, your account is credited 1% of earnings, automatically deposited in your (crypto) wallet.
In messaging, Converse is a simple messaging application with embedded wallets. Users create any number of accounts, and a crypto wallet automagically appears, enabling you to send/receive cryptocurrency or even collect event tickets. Converse flipped the traditional crypto wallet model by embedding it inside a messaging app, elegantly and without obfuscation.
In the money transmission field, several new apps are vying to replicate Venmo’s popularity with a fresh approach. Among them are Beans, Code, and Sling. Even Coinbase has entered the fray with the simple thought of generating a special link that can be shared across messaging apps to enable stablecoin transfers.
What is common to all these lighthouse examples is a voluntary design goal to not force the user to geek out on Web3 from the first encounter. Rather, Web3 is hidden and appears at the right moment, allowing the user to get their feet wet before deciding to venture further.
Blockchain purists might disagree with this approach by stating that everything must be decentralized from the get-go. They argue that, if you sign on with Google credentials, for example, you’re defeating the purpose of decentralization.
However, the counterargument is grounded in user experience best practices: let users take Web3 in incremental doses. Small, familiar ones first, bigger ones later.
If we want early adopters to invite their friends into Web3, we need to let them ease themselves into it by tucking crypto features under a Web2 veneer. You don't typically get too many first chances.
By prioritizing user-centric design, Web3 can truly revolutionize the internet experience, making it more accessible and intuitive for everyone.
In the long run, the popular blockchain protocols that we know today will be little more than stepping stones for developers. They are not legitimate consumer on-ramps. The true on-ramps will be user-friendly apps that will bring in millions of users.
A version of this post was publised in Fortune Crypto, These Web3 companies are embracing Web2 principles to reach users more interested in restaurant rewards than blockchains.
Beyond the Blockchain Infrastructure Layer Wars: Embracing the Interoperable Future of Apps and Services
“Technical people don’t ask the right questions.”
- Henry Kissinger (1923-2023)
In blockchain technology, a heated debate persists surrounding the efficacy of various infrastructure layers. On X (formerly known as Twitter), proponents of Ethereum (ETH) and Solana (SOL) have been engaging in a 'pissing contest' debate, arguing over the merits of their respective platforms. [Here are two links to such discussions: Link1 and Link2]
These infrastructure layers are simply a means to an end, and this debate overlooks an important vision and fundamental aspiration: to become a global interoperable network of blockchains with Apps and services on top. This vision transcends the limitations of individual platforms, fostering a cohesive environment where applications and services can operate seamlessly across diverse protocols.
ETH, SOL, L1s/L2’s: Stepping Stones for Developers, Not Consumer On-Ramps
While leading blockchain protocols such as Ethereum or Solana play crucial roles in the blockchain landscape, they primarily serve as developer tools, enabling the creation of innovative decentralized applications (dApps) or augmenting Web2 ideas with Web3 capabilities.
However, blockchain protocols do not directly cater to mainstream consumers. Instead, they serve as the foundation upon which consumer-facing applications will emerge. The applications, not the underlying blockchains themselves, will act as the real on-ramps for consumers, via user-friendly interfaces and intuitive experiences.
Moving Beyond Pointless Debates
The ongoing debate between vocal Ethereum and Solana enthusiasts often delves into technical minutiae and pedantic discussions over 'degrees of decentralization', transactions finality speeds, scalability factors, fees, validators conditions, governance methods, etc. These debates, while intellectually stimulating, tend to forget the overarching success factor for blockchain technology: to empower individuals to become regular users of blockchain-based applications.
Prioritizing User Experience and Market Reach
As blockchain technology matures, the focus of discussion, attention, and activity should shift from infrastructure layer 'turf wars' to cultivating a rich ecosystem of user-friendly applications that are interoperable across the patchwork layers of the underlying infrastructure. These applications will target diverse market segments, providing tangible benefits and exceptional user experiences.
Revisiting Blockchain's Core Principles
We should not lose sight of the fundamental principles of blockchain technology amidst the noise of the current landscape. Blockchain's inherent value lies in its ability to facilitate peer-to-peer transactions while eliminating the need for unnecessary central intermediaries. At this point of maturity, all leading blockchain protocols effectively achieve this core objective.
Beyond the above core principle, blockchain technology also encompasses mechanism design and smart programming logic as another blockchain 'first principle' of sorts. While each protocol approaches this aspect differently, most have demonstrated this capability.
Consumer Indifference to Blockchain Infrastructure
The average consumer will ultimately care less about the underlying blockchain infrastructure powering their applications. Instead, they will prioritize functionality, convenience, and a seamless user experience.
The field remains wide open for imaginative mainstream consumer applications. These applications may operate on diverse blockchain platforms or even transcend blockchain entirely, utilizing the technology's underlying principles without explicitly exposing it to users.
Let me illustrate with two examples I’m familiar with.
To the user, Blackbird looks like a restaurant loyalty application. Tucked somewhere in a corner of its technology architecture, you will find blockchain technology in the form of unique, non-transferable certificates (NFT-based) that users earn as a status symbol reflecting their customer loyalty activity. Also, in there, you will find a private currency equivalent to airline points, except that rewards gained are redeemable for restaurant perks with very low levels of transaction friction.
In the field of decentralized finance, Prime is a cross-chain prime brokerage that allows users to deposit, borrow, repay, and withdraw cryptocurrency across 8 different chains seamlessly. This sounds like a banal feature when compared to traditional finance where interoperability is taken for granted (albeit with a lot of friction). That said, Prime represents the leading edge of where interoperability exists in blockchain technology.
Let’s Embrace Interoperability and Innovation
Blockchain ecosystem players should move beyond the infrastructure layer wars and embrace a more collaborative approach. Interoperability between blockchains is paramount to achieving the shared vision of a global, interconnected infrastructure. Applications developers should focus on building innovative applications that cater to diverse consumer needs, while infrastructure layers should continue to evolve and adapt to support this growth.
Ultimately, the success of blockchain technology hinges on its ability to empower individuals through user-centric applications that deliver tangible benefits.
The future of blockchain is about the applications that empower users rather than the battle between different layers.
Re-Thinking DAOs as an Evolution of Coops
We should stop trying to force DAOs to exist based on their current path of evolution if they want to be a positive part of the blockchain future.
There is no doubt that most DAOs from the cohort that mushroomed during the 2020-2022 period are floundering, or being very loosely successful.
Yet, some pundits continue to profess a type of analysis that obscures instead of enlightens. Machiavelli for DAOs: Designing Effective Decentralized Governance struck me as a very unrealistic opinion about how to design decentralized governance by espousing Machiavellian principles.
One of the biggest problems is when we see DAOs as a lever to eliminate the need for human management. This is a naive and misguided assumption. No organization can run on autopilot, and DAOs are no exception. Even when you inject the strong community component that is always part of DAOs, communities also need to be managed with human intellect. In fact, DAOs can be even more difficult to manage than traditional organizations, due to their decentralized nature and the diversity of their shot-gun stakeholders.
We need to stop trying to force decentralized organizations as a panacea for something that doesn’t need it. And we need to be realistic about what’s viable.
There is validity in rethinking the way we design and implement DAOs towards more simplicity, not complexity. We need to move away from the idea of DAOs as completely autonomous organizations, and instead think of using DAO constructs as a complement that espouses the novelties of blockchain and cryptocurrency. Maybe DAOs are meant to be a complement to something else but not an entirely standalone thing.
I don’t mean that we need to throw the whole concept away. There are some very good embedded ideas, at the high levels:
Decentralization is a good anti-single point of failure.
Automation with embedded smart contracts does bring operational efficiency.
Community/user voices with decision-making influence have their benefits.
Giving back parts of the economic gains to participants that contributed to wealth creation is the right thing to do.
The “autonomous” part in the DAO vocabulary is perhaps the most misleading, misguided, and certainly the weakest part of the equation.
Management by committee, delegation, or populist votes is a terrible idea. Conflating blockchain consensus mechanisms with human decision-making is blasphemy against human intelligence and decades of sound management practices.
Voting on decisions, when you have an economic or ideological stake, is not a bad idea, even if it’s only a directional vote that could influence a future decision, but thinking that this is sufficient for running organizations or projects is a naive assumption.
On the regulatory side, being “autonomous” doesn’t absolve an organization (or its instigators) from the rule of law as set by governments or regulatory authorities.
Maybe DAOs could be applied when there is predictable repeatability, no issues, no surprises, and when a given system is stable. These difficult simultaneous conditions narrow DAO’s applicability field tremendously.
The cooperative (Coop) corporate business model is the closest to the DAO concept. I think the industry should work more diligently to extend and adapt the Coop model instead of trying to push DAOs as we know them today.
Source: https://coopcreator.ca
Platform cooperatism is a concept that was recently introduced. It is described as “businesses that sell goods or services primarily through a website, mobile app, or protocol.”
This article, ‘Staking’ Identities: Looking at the Practicalities of Transforming DAOs Into Co-ops looks at the similarities between DAOs and Platform Cooperatives.
We can draw a lot of inspiration from the cooperative Coop model. At their core, coops are businesses that are owned and democratically controlled by their members. That happens to be the primary goal of DAOs, which is why the match is worth exploring seriously.
By combining the best of DAOs and the best of coops, we can create a new type of organization that is democratic, equitable, and resilient.
12 Things the Crypto Industry Needs to Get Right
It's going to take a long time to get back on track
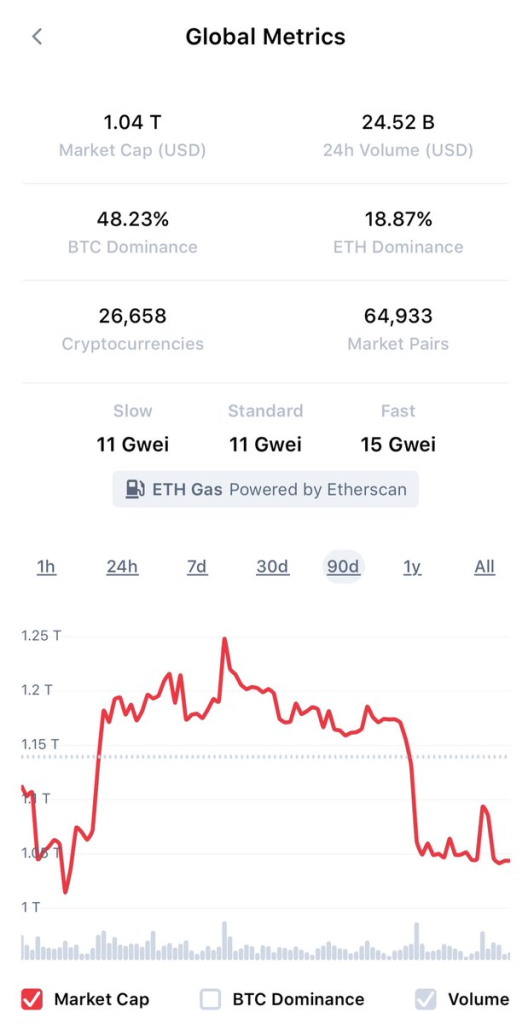
It’s the end of summer and return to work or school for many people. Crypto has had a boring summer, no matter how you cut it. In terms of prices, we’re pretty much where we were 90 days ago, roughly. (See chart below)
However, beyond that quantitative metric, the industry malaise will continue as long as we have a hostile US regular (the SEC). Sadly, the crypto industry has a lot of headwinds to fight through. Every bit of good news is quickly tempered by regulatory realities.
The non-US market that wants to shrug off the SEC is not so immune to what happens in the US. The US is still that locomotive engine that needs to go full speed to power the rest of the industry. So, we can't just depend on the rest of the world to pave the way on its own.
What could lift things permanently is a lot of things:
1. SEC change of regime and / or change of rhetoric
2. US Congress passing some law(s)
3. Bridges working seamlessly between L2s & from Ethereum to non EVM chains (eventually it should be just “VM”,- the blockchain as one virtual machine)
4. Many more consumer apps with a dead-easy mainstream user experience, leading to millions of committed users that use these apps daily
5. Spot ETF products for Bitcoin & Ethereum (a few of them)
6. Lower gaps between promise and reality for any new / existing blockchain projects (ie lower the hype)
7. No extraordinary bad actors for a full year (ie no significant scams or security exploits)
8. Moving the conversations away from the technical realm that currently dominates (speeds & feeds won’t matter much, but interoperability & user experience will matter). Degrees of decentralization debates are overdone.
9. Players consolidation at the L1 level which is Ground zero (there are far too many competing & non-interoperable L1’s & that works directly against much needed network effects) [related to #3 & #9]
10. Established companies adoption of blockchain / crypto not in an opportunistic way, but more fundamentally
11. Emergence of better / newer / more (human) role models in the crypto space
12. Crypto techies that can better explain the business aspects and applications of what they are building; less tinkering, more useful tech. We also need more no-code tools to put in the hands of non-tech users.
Of course, all these points are being worked on. That’s the good news.
The bad news is that it will take a while to get there as these aren’t going to be realized overnight.
A Critical Perspective on Ethereum: Too Much Tinkering
The tinkering ratio of output can be improved to yield more mainstream products
I'm writing this critique with a deep and long historical perspective on Ethereum because I want Ethereum to succeed better. I’d like its ecosystem to get stronger. I’d like its apps and services to be more useful. I’d like its end-user experiences to be on par with what the mainstream consumer expects.
At a time when many other L1 blockchain infrastructures are struggling for growth, Ethereum has a chance to clean up and solidify its position as the preeminent blockchain infrastructure.
Whether changes happen or not depends to a great extent on what the Ethereum community does or doesn’t do. There is a limit to what the market can do to pick up the pieces and innovate on top of what is handed to them.
This comes at a time when a large part of the Ethereum community is getting ready to re-assemble in Waterloo where the first ETH Global event took place six years ago. I participated in that event, wrote From Waterloo to Zug, Retracing Ethereum’s Journey and made a presentation chronicling the then-emerging Ethereum ecosystem.
I’d like to talk about what Ethereum can do better. So, I’m going to focus on some parts that could be improved, in order to maximize Ethereum’s potential.
There is no need to extol Ethereum’s strengths, as you all know them. But sometimes your strengths create a weakness. So we can start there.
One of Ethereum’s strengths is the diversity of its ecosystem and how much development activity there is around it. It is undoubtedly the most vibrant laboratory for blockchain innovation.
However, that strength has become a weakness because there is too much TINKERING in that ecosystem.
Tinkering is not bad because it can lead to great things as you iterate. But when I said “too much tinkering”, I meant on a relative basis.
Tinkering as a ratio of output can be improved. This means that we don’t necessarily need less tinkering, but we need more tinkering that results in fully deployable and usable solutions. And not just at the technical level. We need more end-user applications with user-friendly, mainstream-appeal types of applications.
If your tinkering doesn’t produce an end result, do you know what happens?
Other chains take your half-baked ideas and they add the last mile to it, and they deliver something usable. Sounds familiar?
One of the drawbacks of too much tinkering is that we tend to forget about tuning the end-user experience.
Of course, the first level of the Ethereum ecosystem is mostly comprised of developers, and that’s a great thing. Developers typically work on infrastructure or they work on services for other developers to build applications on, or they work directly on applications.
The part that needs the most improvement is the last part, the part that touches the end user.
If Ethereum wants to be in the hands of one billion users, it needs to think more about the importance of mainstream user experiences. The mainstream user wants SIMPLICITY first, and two or three clicks to get impressed and hooked. That challenge, by the way, doesn’t only apply to the Ethereum community. It does also matter for the entire blockchain industry. I recently wrote, What The Blockchain Industry Can Learn From the Popularity of Artificial Intelligence pertaining specifically to the user experience.
Here are two related parts where Ethereum can improve.
First, the Ethereum development ecosystem needs more product managers. Product managers focus on getting the product to the market in its most usable form. Sadly, sometimes, they are the ones who realize that at one point, you need to shoot the engineers in order to get the product out. Product managers obsess about the user experience, user flows and user interactions. Product managers understand how to lay out a roadmap and prioritize features rollout accordingly.
Second, the L2 layers fragmentation is another strength-turned-weakness. L2’s have been undoubtedly beneficial to Ethereum’s scalability, but from a user perspective, the experience is not ideal, because of the switching friction. As a user, imagine if you had to switch browsers to access different parts of the web. It would be unthinkable, yet we ask Ethereum users to decide which L2 to choose from. Furthermore, we make them jump through hoops and take security risks to bridge from one network to another if they seek to move assets across L2’s.
I don’t have a solution for this fragmentation, and some believe it’s not an issue, but I do think it is. Therefore, I’m just laying out the challenge to elevate its visibility and importance. When there is less friction, there is more adoption.
I realize that the Ethereum ecosystem is obsessed with an extreme form of decentralization at all levels of the stack. But that also creates challenges, because as you unbundle various pieces in order to decentralize the system, you then need to re-bundle everything to properly assemble a solution. Then, you need a lot of coordination and making sure that many parts work together at the same level of readiness and response, and that’s not always so easily achieved.
This challenge was validated in Vitalik’s last essay, The Three Transitions where he advocates there are three essential capabilities that need to work together in Ethereum: L2 scaling, wallet security, and privacy. There is nothing new with these individual features as they were part of the early vision of the Ethereum blockchain. However, with increased decentralization, there are increasing degrees of complexity that compound when you start to implement these three prongs simultaneously.
Ethereum is approaching its ten-year mark on its original inception. It’s time that we polish the ongoing tinkering in its base infrastructure and services so that apps can prosper on top of it.
I’m looking forward to seeing more product managers and entrepreneurs drive the Ethereum ecosystem in addition to the base technology developers who are obsessed with technology tinkering.